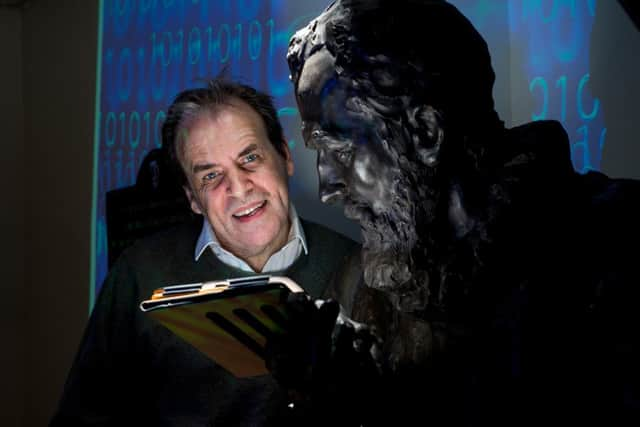
Bill Buchanan: The risks of the Cyber Age


We are now living in one of the most amazing epochs of human history: The Cyber Age.
But the world we have created online is a fragile one. In recent years we have seen internet giants like Skype, Amazon, Google and Dropbox all suffer outages. We should all, thus, be aware that our increasing dependence on internet services and Cloud computing does bring many risks.
Advertisement
Hide AdAdvertisement
Hide AdAs a small country, Scotland can take full advantage of this new Age, but there are many risks.

LARGE-SCALE DATA LEAKAGE
One of the greatest risks to our citizens is in data leakage, as data is increasingly a target for cyber criminals. The target, too, is not just credit card details.
Stealing medical records, for example, is an attractive criminal business, as the data gained could be worth at least ten times the value of credit card data on the black market. The number of healthcare data breaches rises at a worrying pace. Since last year, medical identity theft incidents increased 21.7 percent, and there are forecasts that healthcare breaches will keep increasing in the near future, due to the potential economic gain and digitization of records.
Forbes, too, have recently reported, that, in less than one year there has been nearly 96 million records were stolen (Community Health Systems (4.5 million), Anthem (80 million), and Premera (11 million)).
Leaked details can include included financial records, history of addresses, names of family relatives, foreign trips, and contacts with foreign nationals.
The opportunity for embarrassment is highlighted by the Ashley Madison hack, and where the company thought that they had protected users passwords, but sloppy software development methods allowed cipher crackers to crack 11.2 million passwords. Users too need to take some responsibly for their security, and can’t always assume that companies will use best practice.
INTERNET OF EVERYTHING
The next wave of online advancement will expose our lives to much greater threats, with billions of touch points. The Internet of Everything (sometimes called the Internet of Things) refers to an internet where many physical objects will connect to the Internet. This includes many things found in your home such as wi-fi kettles, wi-fi controllable lights, electronic locks, and home entertainment systems.
These systems, though, are often designed for simplicity in setting things up, and where security is not a key focus. Many researchers have found these devices to be flawed in some way, such as for the electronic locks which can be reset using a “reset to default” signal.
Advertisement
Hide AdAdvertisement
Hide AdThe increasingly connected world has now made it into our vehicles, and one must wonder if car manufacturers really understand how to secure their cars from cyber criminals. With 42 per cent of cars stolen in London last year without a key being used, one must wonder if we can patch our cars as fast as we patch our mobile phone. The recent hacks in cars have shown that the car industry is struggling to cope with the new range of threats.
FAILURE OF INFRASTRUCTURES
Key services are often interconnected and if one part of the chain fails, the rest of the interconnected system can then trip. Perhaps a pointer to the problems that an outage can cause is the Northeast blackout on 14 August 2003, and which affect 10 million people in Ontario and 45 million people in eight US states.
It was caused by a software bug in an alarm system in a control room in Ohio and where some foliage touched one of the supply lines, and caused an overload of them. The bug stopped the alarm from being displayed in the control, and where the operators would have re-distributed the power from other supplies. In the end the power systems overloaded and started to trip, and caused a domino effect for the rest of the connected network. Overall it took two days to restore all of the power to consumers.
As we become more dependent on electronic versions of our public services it becomes important, especially in areas such as health and social care, to have robust infrastructures that can cope with outages.
VERDICT
So the Cloud we have created, and which we are all dependent on, and where we link to services over the Internet, is not as robust as we think it is. The Internet too is not quite as distributed as it was designed to be, and we still rely on key physical locations for data and for networked connections. Any problems in these, can cause the whole infrastructure to fall like dominos.
Scotland, unfortunately, has quite a few choke-points, and where a failure in these could cause large-scale damage to the economy and for the lives of our citizens. We are also an increasingly connected world, so problems in our own data centres and ones in other regions of the world can cause problems here. It would be impossible to roll-back the services we have created.
Scotland is not immune from large scale data losses, and our business need to understand how they protect information from large-scale data loss.
On the positive side there is also a growing economy within Scotland focused on cyber security defence, and most of the top companies, along with innovative SMEs, have a strong footprint in Scotland, especially to support our key industries, such as the finance sector, and energy.
Bill Buchanan is Professor of Computing at Edinburgh Napier University and leads The Cyber Academy, which provides international leadership in Cyber Security.